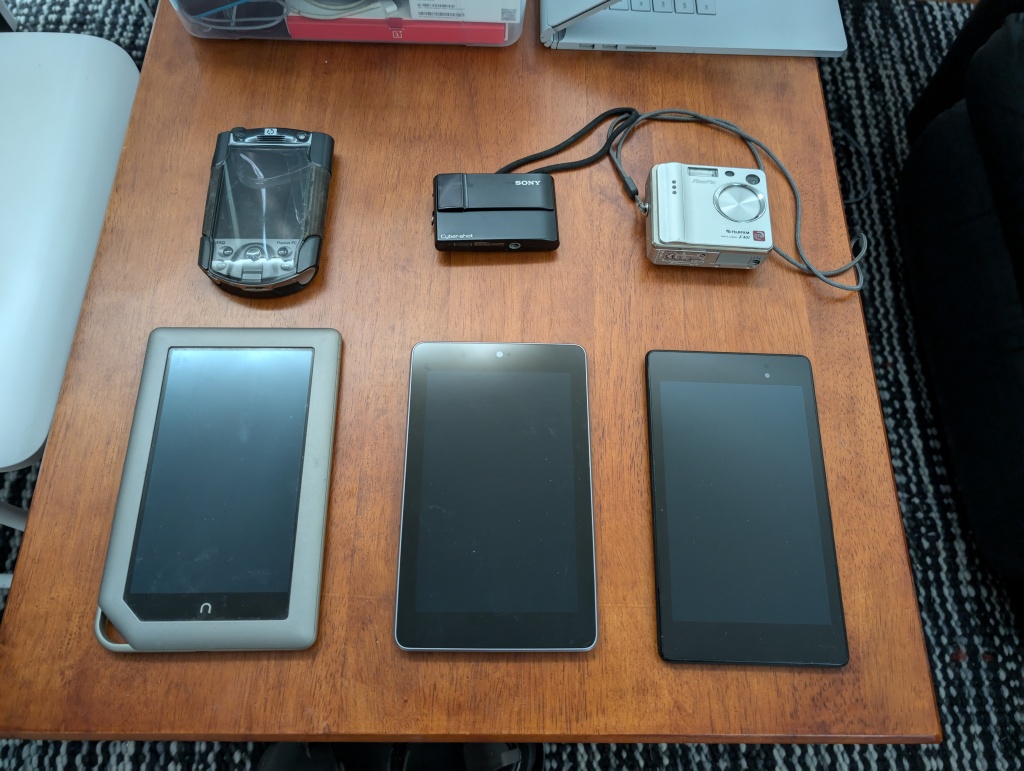
Found while unpacking boxes last night:
Shown above, top to bottom, left to right:
- Sony PSP-2000: Handheld game console. Mostly used for playing emulated SNES games. Covered unlocking and installing custom firmware in this 2008 blog post. Battery failed ~5 years ago.
- Nintendo 2DS XL: Handheld game console. Also mostly used for emulated games.
- Anbernic RG350M: Handheld game console. Only used for emulated games. I liked the build quality but the metal put strain on my wrists.
- Nokia N810: “internet tablet” (smartphone precursor). Used quite a bit before I got my first Android phone. Battery failed at some point, but I only discovered the failed battery last night.
- Cowon iAUDIO X5 60GB: Portable media player with a 60GB spinning rust (!?!) hard drive. Note: Physical disks in media players made sense at the time because flash-based players had extremely limited capacity. Had Rockbox installed. Covered in this 2006 blog post. My patches for the Rockbox Game Boy emulator were covered in this 2005 blog post.
- RIM Blackberry (model unknown): Old work phone that I never liked and rarely used. Covered in this 2007 blog post.
- Apple iPod Classic 120GB: Portable media player. I didn’t like this thing, rarely used it, and can’t remember how I got it. Maybe a gift or reward?
- Samsung Galaxy S II (SGH-T989): Used CyanogenMod to add features, ditch the awful Samsung Android skin, and extend the support by several years.
- Google Nexus One: My first smartphone without a keyboard. I liked it, but the screen was too small, the capacitive buttons were hard to press, and the trackball mostly just got in the way.
- OnePlus One: Good price/performance at the time. Ran Cyanogen OS out of the box. Novel textured back. Awful camera.
- OnePlus 5T: Great phone at release. Still decent even now (for me, at least). I liked the rear fingerprint scanner and the slim bezels. Bad camera. I plan to install LineageOS and continue using it for non-phone stuff (drone remote control, dubious apps, etc).
Not shown (lost, recycled, or still buried in boxes):
- Samsung SGH-t809: My first cell phone. Bought in 2006. Battery failed ~10 years ago. Covered in this 2006 blog post.
- Motorola Cliq: My first Android smartphone. Not a very good device in retrospect.
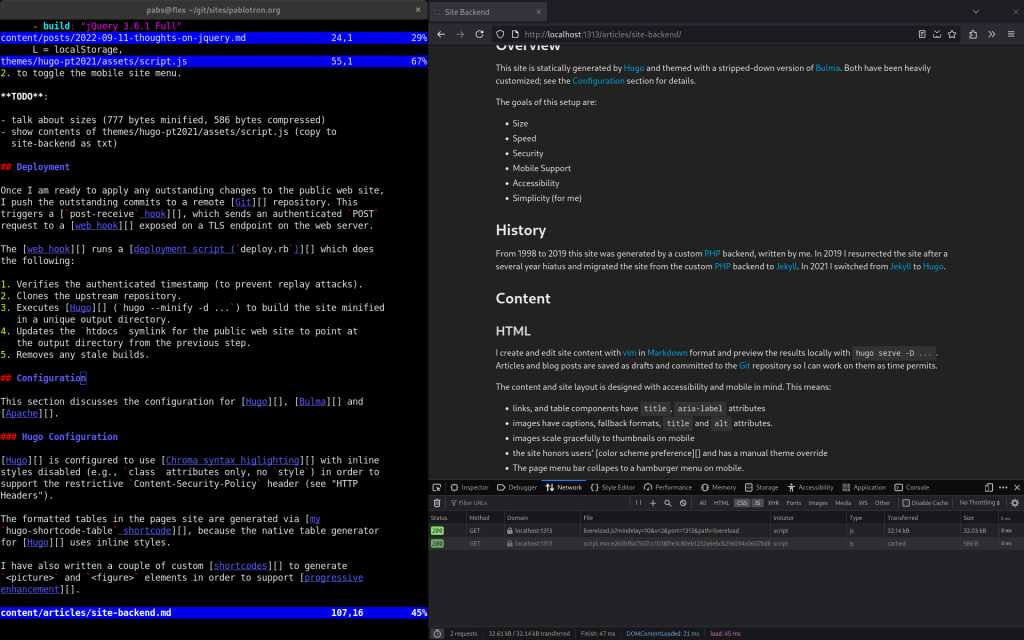
- Barnes and Noble Nook Color: Immediately installed CyanogenMod and used as a cheap Android tablet.
- Google Nexus 7 (2012) and Nexus 7 (2013): I liked the form factor of these tablets. The original model was a bit slow so I upgraded to the 2013 model at release and used it daily until it stopped booting.
Current gadgets:
- Google Pixel 8 Pro: Current smartphone and the first one I’ve owned that is waterproof. I’m very happy with it. Great camera. Screen is large enough to read eBooks. Used to take the picture above.
- Samsung Galaxy Tab S5e (Wi-Fi): Current tablet. Immediately installed LineageOS because I prefer it to One UI. I use it to read eBooks and with the detachable keyboard as a second laptop.
- PowKiddy RGB10 Max: Current handheld game console. Only used for playing emulated games. Lighter and has a larger screen than the Anbernic RG350m shown in the picture above. Rarely used.
- Sony WF-1000XM4: Current Bluetooth headphones. I use these daily for meetings and to listen to music and to watch TV shows past my bedtime. Great audio quality, battery life, and charging speed. My only complaint is the phone app tries to railroad you into an unnecessary Sony account during installation.
Update (2024-07-26): I found the Nook, Cliq, both Nexus 7 tablets, an iPaq, and two digital cameras. Everything except the Cliq is shown below:
Those are some massive bezels!